US sanctions operators of “free VPN” that routed crime traffic through user PCs

MALICIOUS BOTNET TECHNOLOGY —
911 S5 residential proxy service was comprised of 19 million IP addresses.
Getty Images
The US Treasury Department has sanctioned three Chinese nationals for their involvement in a VPN-powered botnet with more than 19 million residential IP addresses they rented out to cybercriminals to obfuscate their illegal activities, including COVID-19 aid scams and bomb threats.
The criminal enterprise, the Treasury Department said Tuesday, was a residential proxy service known as 911 S5. Such services provide a bank of IP addresses belonging to everyday home users for customers to route Internet connections through. When accessing a website or other Internet service, the connection appears to originate with the home user.
In 2022, researchers at the University of Sherbrooke profiled 911[.]re, a service that appears to be an earlier version of 911 S5. At the time, its infrastructure comprised 120,000 residential IP addresses. This pool was created using one of two free VPNs—MaskVPN and DewVPN—marketed to end users. Besides acting as a legitimate VPN, the software also operated as a botnet that covertly turned users’ devices into a proxy server. The complex structure was designed with the intent of making the botnet hard to reverse engineer.
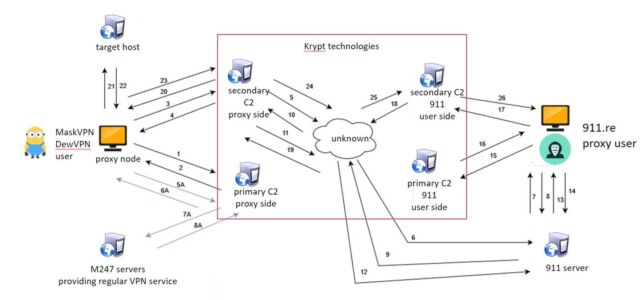
Enlarge / An illustration of showing how the DewVPN and MaskVPN caused devices to connect to a command-and-control server located in the back end of an entity called Krypt Technologies.
University of Sherbrooke
MaskVPN and DewVPN connected devices to the type of server legitimate VPNs use to obfuscate the originating IP address and route traffic through an encrypted tunnel. At the same time, hidden functionality established a permanent TCP socket to a botnet command-and-control server. University of Sherbrooke researchers wrote:
This TCP connection is made to the C2 servers of the 911.re backend infrastructure and renders the node available for connections through the 911.re interface. A heartbeat process is in place to ensure the node is listed as available. At no time, there is direct connection between the infected node and the 911.re paid subscriber even when the node is selected, and traffic passes through. All the network traffic is always routed between the C2 servers that are USA based, reducing the risk of anomaly detection by IDS or IPS systems. Mask VPN and Dew VPN are using a custom implementation of the open-source OpenVPN.
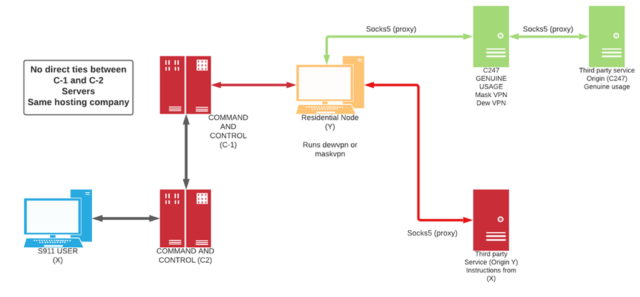
Enlarge / Illustration showing how traffic of 911 users was routed through residential IP addresses.
University of Sherbrooke
The research led to an investigation by KrebsOnSecurity that uncovered Yunhe Wang of Beijing as one of the individuals who registered domains used by the 911[.]re infrastructure.
Wang was one of three people sanctioned on Tuesday. Treasury officials said that Wang was the registered subscriber of services used both by 911 S5 and the MaskVPN and DewVPN operations, an indication they were relying on some of the same resources reporter Brian Krebs did. They also named Jingping Liu as a co-conspirator for allegedly helping Wang launder virtual currency and other proceeds generated from the 911 S5 enterprise. The officials further named Yanni Zheng, for allegedly acting under the power of attorney for Wang and participating in business transactions and making purchases and payments on Wang’s behalf, including for a luxury beachfront condominium in Thailand.
“These individuals leveraged their malicious botnet technology to compromise personal devices, enabling cybercriminals to fraudulently secure economic assistance intended for those in need and to terrorize our citizens with bomb threats,” said Under Secretary Brian E. Nelson. “Treasury, in close coordination with our law enforcement colleagues and international partners, will continue to take action to disrupt cybercriminals and other illicit actors who seek to steal from US taxpayers.”
The treasury officials also sanctioned three Thailand-based businesses: Spicy Code Company Limited, which purchased additional real estate properties for Wang, and Tulip Biz Pattaya Group Company Limited and Lily Suites Company Limited, both of which were purchased by Wang.
The officials said the 911 S5 botnet comprised roughly 19 million IP addresses. Criminals used it in “tens of thousands of fraudulent applications” related to coronavirus relief scams that resulted in the loss of billions of dollars to the US government. The IP addresses compromised by the service were also linked to a series of bomb threats made throughout the United States in July 2022.
Under the designations, all property of individuals and businesses located in the US or in the possession or control of US persons must be blocked and reported to the Treasury Department’s Office of Foreign Assets Control. The sanctions also prohibit dealings by anyone in the US involving any of the blocked property. People who run afoul of the sanctions may themselves be exposed to designation.
Tuesday’s action comes six days after researchers from Google-owned security firm Mandiant said that the use by China-nexus threat actors of residential proxy networks known as operational relay box networks was hindering traditional means of tracking and defending against cyberattacks. Mandiant researchers urged defenders to adopt new approaches.
“Mandiant asserts that the best way to rise to the challenge posed by ORB networks is to stop tracking espionage C2 infrastructure as an inert indicator of compromise and start tracking it as an entity with distinct TTPs,” the researchers wrote. “We no longer operate in the world of “block and move on” where IPs are part of APT’s weaponization and C2 kill chain phase.”